SAML merged the following parallel security efforts into a single technology and was submitted to Organisation for the Advancement of Structured Information Standards (OASIS):
- Security Services Markup Language (S2ML)
- Authentication Markup Language (AuthML)
Main features:
- Development of federated systems
- Enable seamless integration
- Exchange of information among different security systems
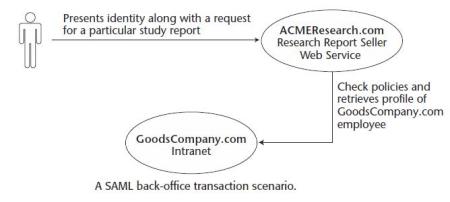
- Backoffice Transaction
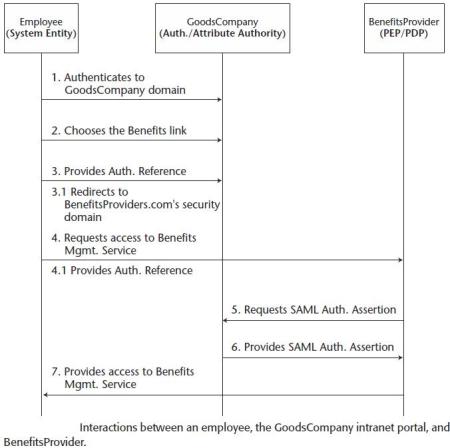
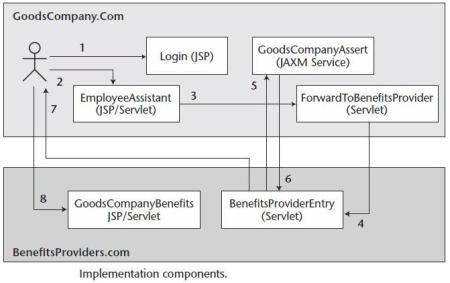
- Single-Sign-On (SSO) – user’s ability to authenticate in one security domain and to use the protected resources of another security domain without re-authenticating
- XML-based framework for security-related information over Internet

SAML specification consists of the following set of documents:
- Assertions and protocol – defines the syntax and semantics for XML-encoded SAML assertions, protocol requests, and protocol responses.
- Binding and profiles – defines the frameworks for embedding and transporting SAML assertion requests and responses.
- Security and privacy considerations – to provide information to implementers of SAML systems about possible threats, and security risks to which a SAML-based system is subjected.
- Conformance program specification – defines a SAML conformance system that isaimed toward achieving compatibility and interoperability among all applications that implement SAML.

- XML-based frameworks for exchanging security information in the form of an assertion or facts about subjects.
- A subject has an identity in some security domain. This subject can be an identified person or it can be some code in which assertion may be required so that the code can be allowed to execute on a system.
- A SAML authority or an issuing authority issues the assertions.
- The SAML authority can be performed by the following parties:- 3rd party security providers such as Microsoft with Passport- Individual businesses as security provider within Federations such as AMEX, VISA
- Three types of core assertions:- authentication assertion- authorisation assertion- attribute assertion
- Assertions can be digitally signed using XML Signature as specified by the SAML profile of XML Digital Signature.
- Elements of all assertions:- Issuer and Issuance timestamp- Assertion ID- Subject such as name and security domain which the subject belongs to - Advice – additional information that the issuing authority may wish to provide to the relying party in regards to how the assertion was made eg. evidence or proof of assertion claims.
- Conditions – optional element as its validity id dependent upon the evaluation of the conditions provided. Conditions can be as follows:- + Validity period within which the assertion remain valid after which the assertion would expire + Audience restrictions information, which includes relying parties to whom the issuer of this assertion is liable in terms of accuracy or trustworthiness + Target restrictions information, which includes targeting relying parties for which the authority has issued this assertion. If consuming party is not the target party then assertion must be rejected.

More Here
Courtesy:http://lamyk.wordpress.com/2010/06/17/security-assertion-markup-language-saml/