Single sign-on is an authentication method that allows users with a domain account to log on once to a client computer by using a password, and then gain access to remote servers without being asked for their credentials again. See more details here for Windows Server 2008 and here for Windows Server 2008 R2.
On the client-side SSO are currently available for Windows XP with SP3, Windows Vista and Windows 7.
Configure SSO on the server-side
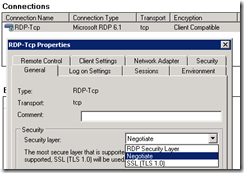
To configure SSO on the server-side (Windows Server 2008 Terminal Services or Windows Server 2008 R2 Remote Desktop Services), set the option “Security layer” to either “Negotiate” or “SSL (TLS 1.0)”:
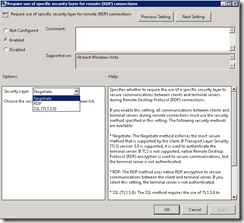
Best practice would be to configure this in a common GPO for all Remote Desktop Services servers in the domain:
This setting resides under Computer Configuration->Policies->Administrative templates->Windows Components->Terminal Services->Terminal Server->Security.
Configure SSO on the client-side
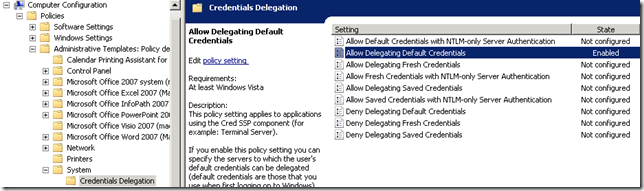
Using a common GPO would also be the best practice to deploy the client settings needed for SSO to work.
The “Allow Delegating Default Credentials” resides under Computer Configuration->Policies->System->Credentials Delegation:
The “Allow Delegating Default Credentials” resides under Computer Configuration->Policies->System->Credentials Delegation:
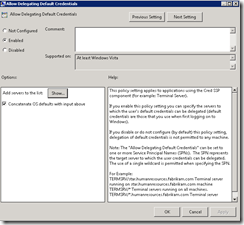
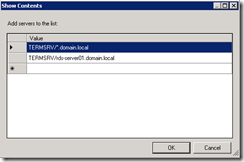
Enable “Allow Delegating Default Credentials”, press the “Show”-button and either specify the domain pre-fixed with * to allow delegation to all servers in the domain, or specify specific servers:
Next, create a RDP-file and deploy this file to the client computers.
Before deploying the file, open it in a text editor, e.g. Notepad, and add the following line: enablecredsspsupport:i:1
This will enable SSO for the RDP-file.
Before deploying the file, open it in a text editor, e.g. Notepad, and add the following line: enablecredsspsupport:i:1
This will enable SSO for the RDP-file.
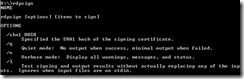
I would also recommend to sign the RDP-file with a Code Signing certificate. This can be accomplished using the utilityrdpsign.exe:
Sample signing:
When a RDP-file are signed, the following will be added to the bottom of the file:
signature:s:AQABAAEAAADBCgAAMIIKvQ……..
More Here
Courtesy:http://blog.powershell.no/2009/12/25/single-sign-on-to-remote-desktop-services/